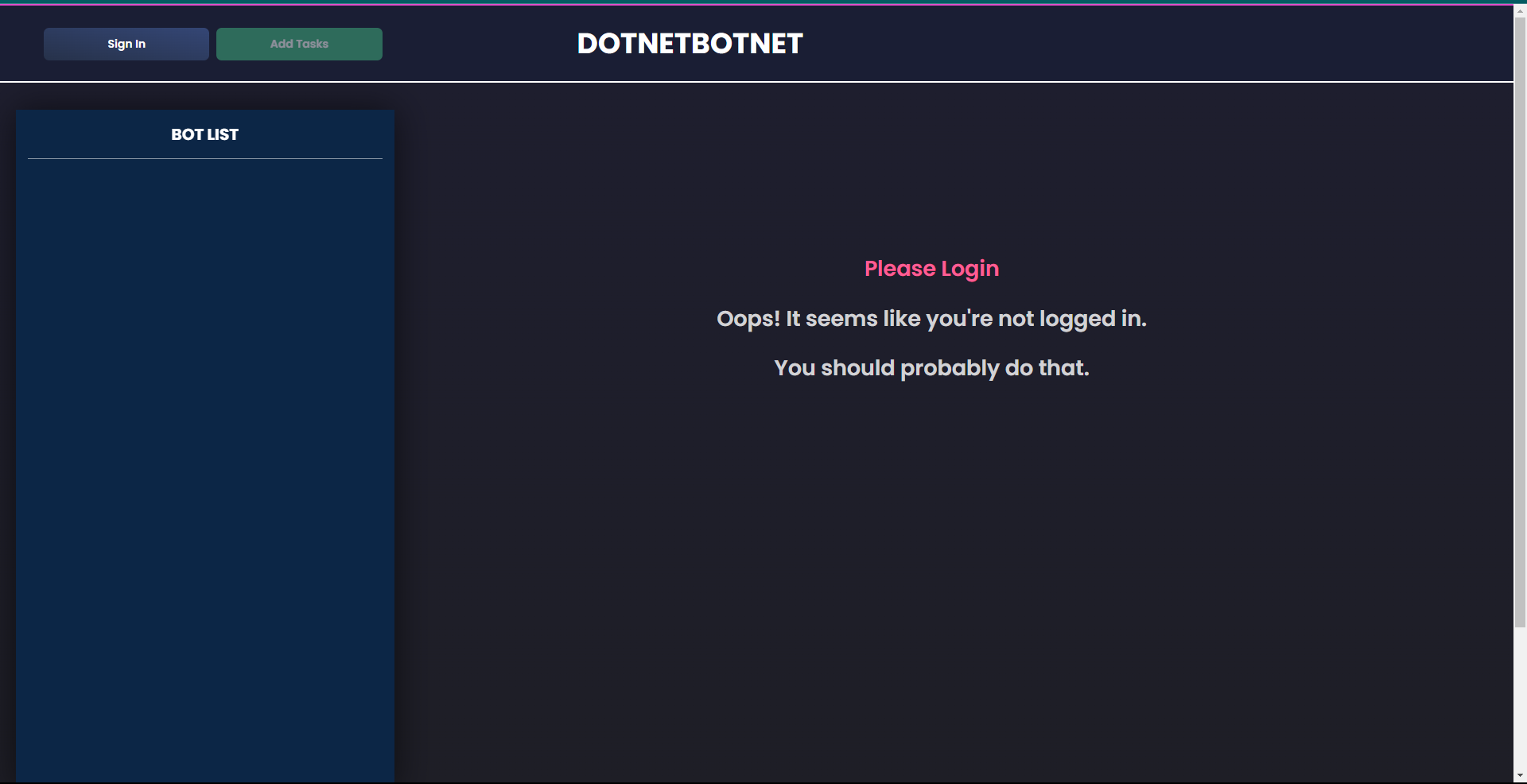
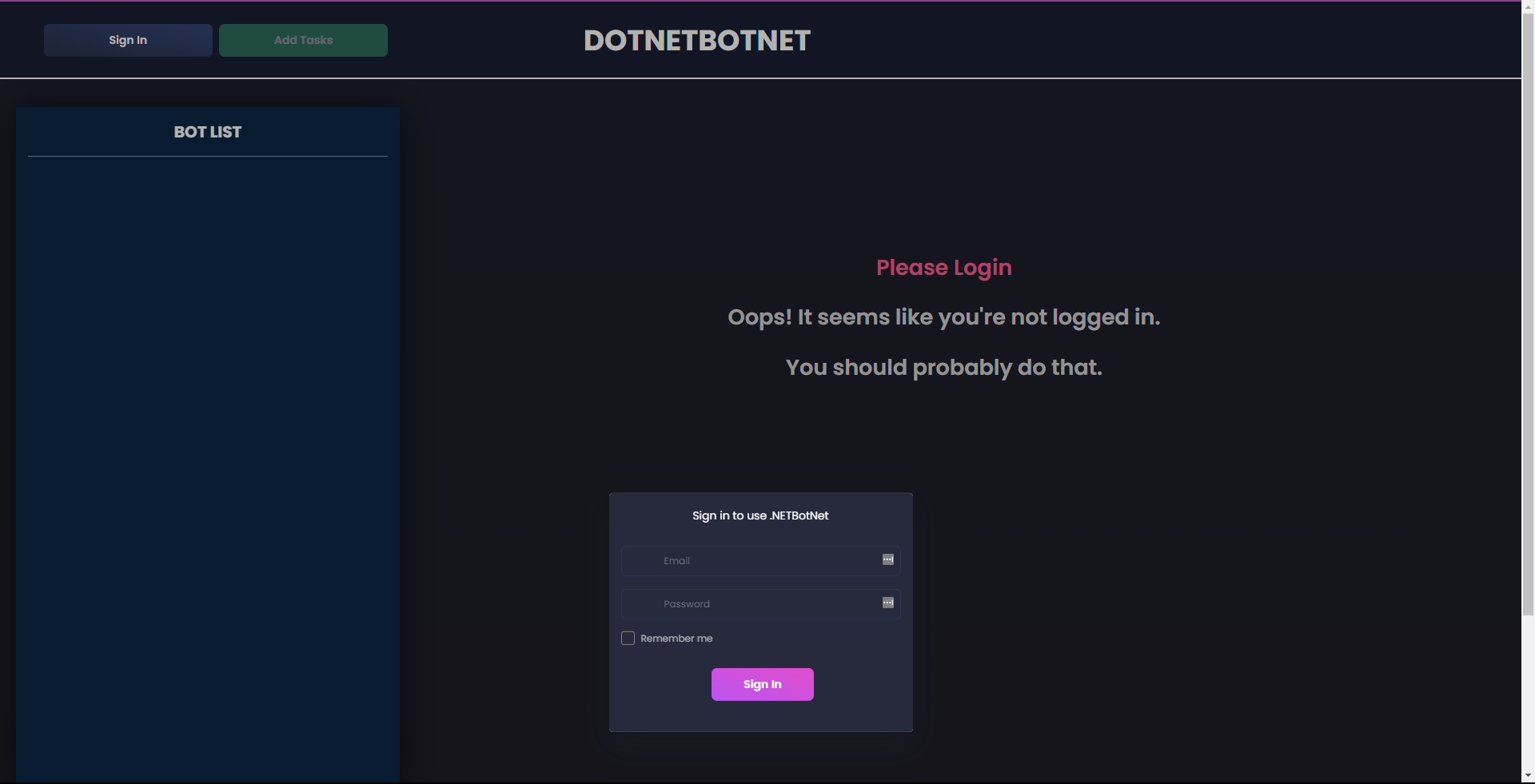
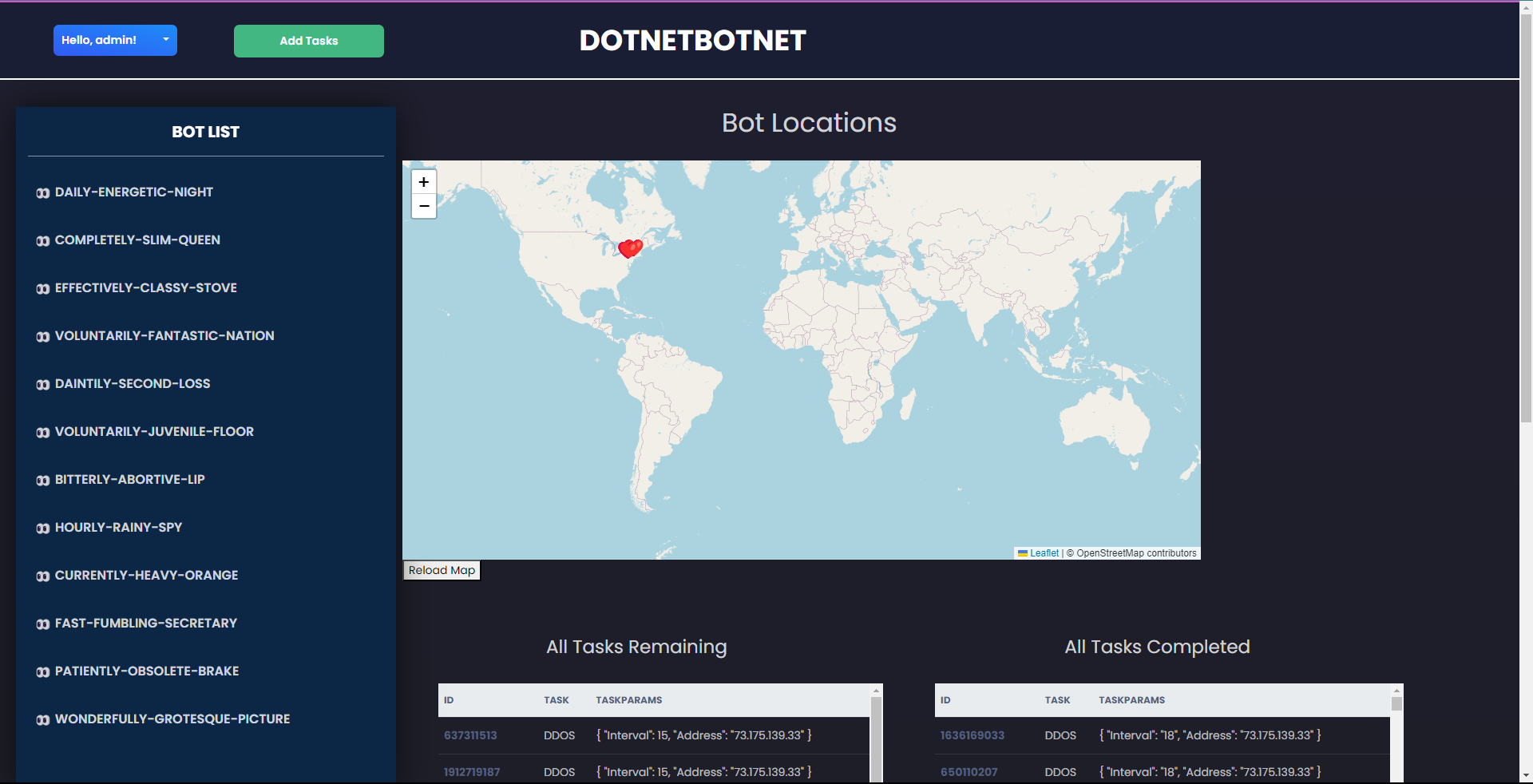
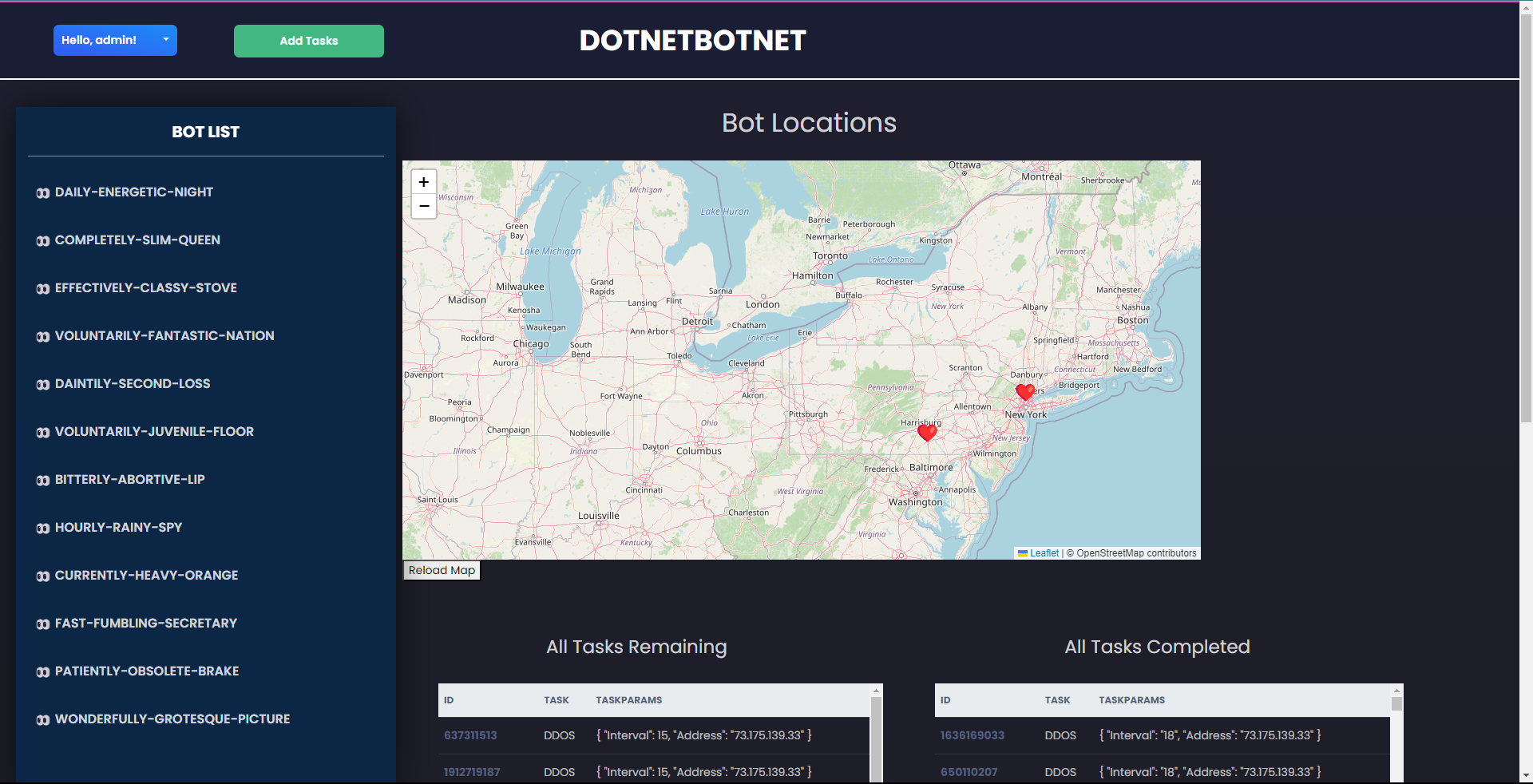
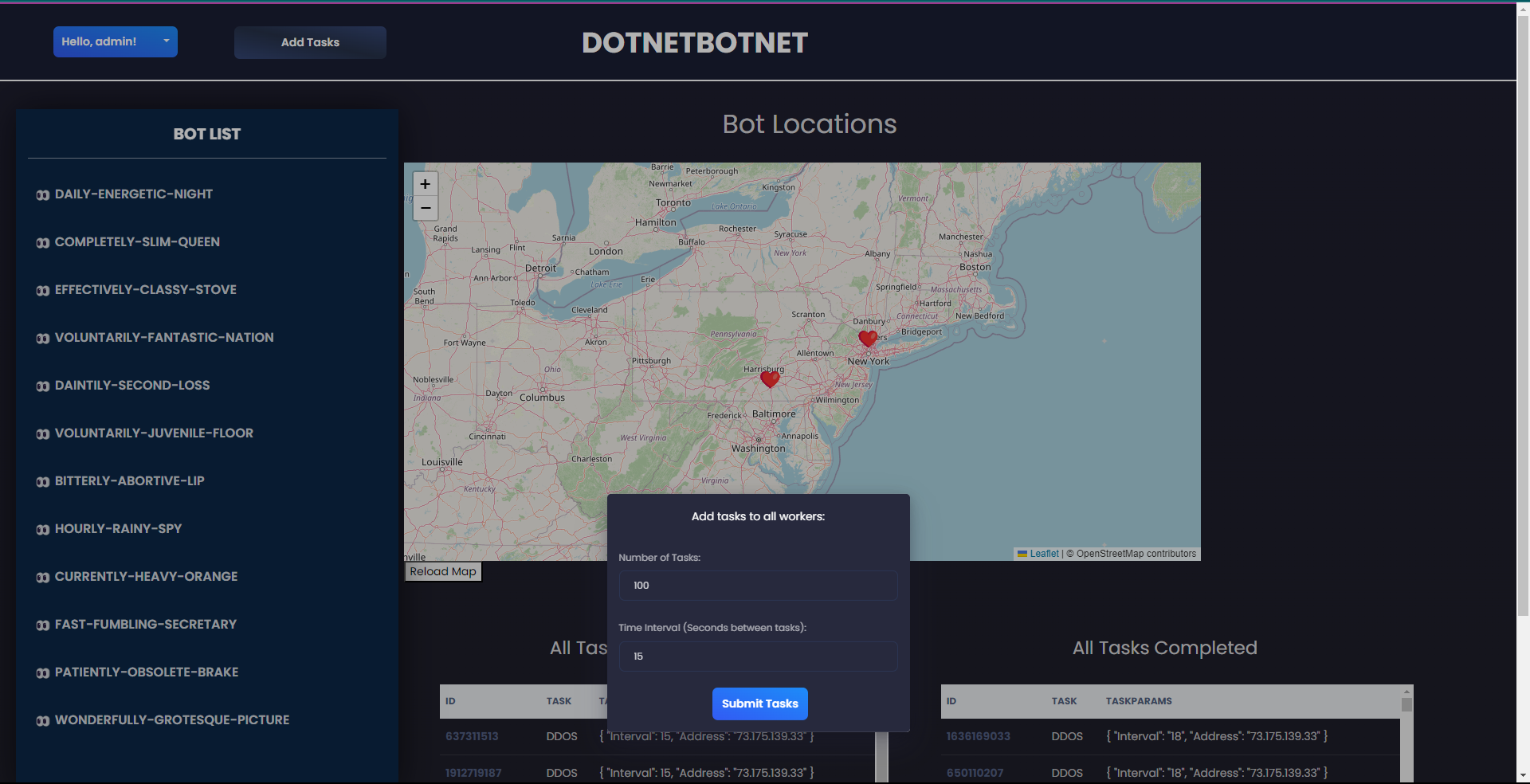
About .NETBotNet
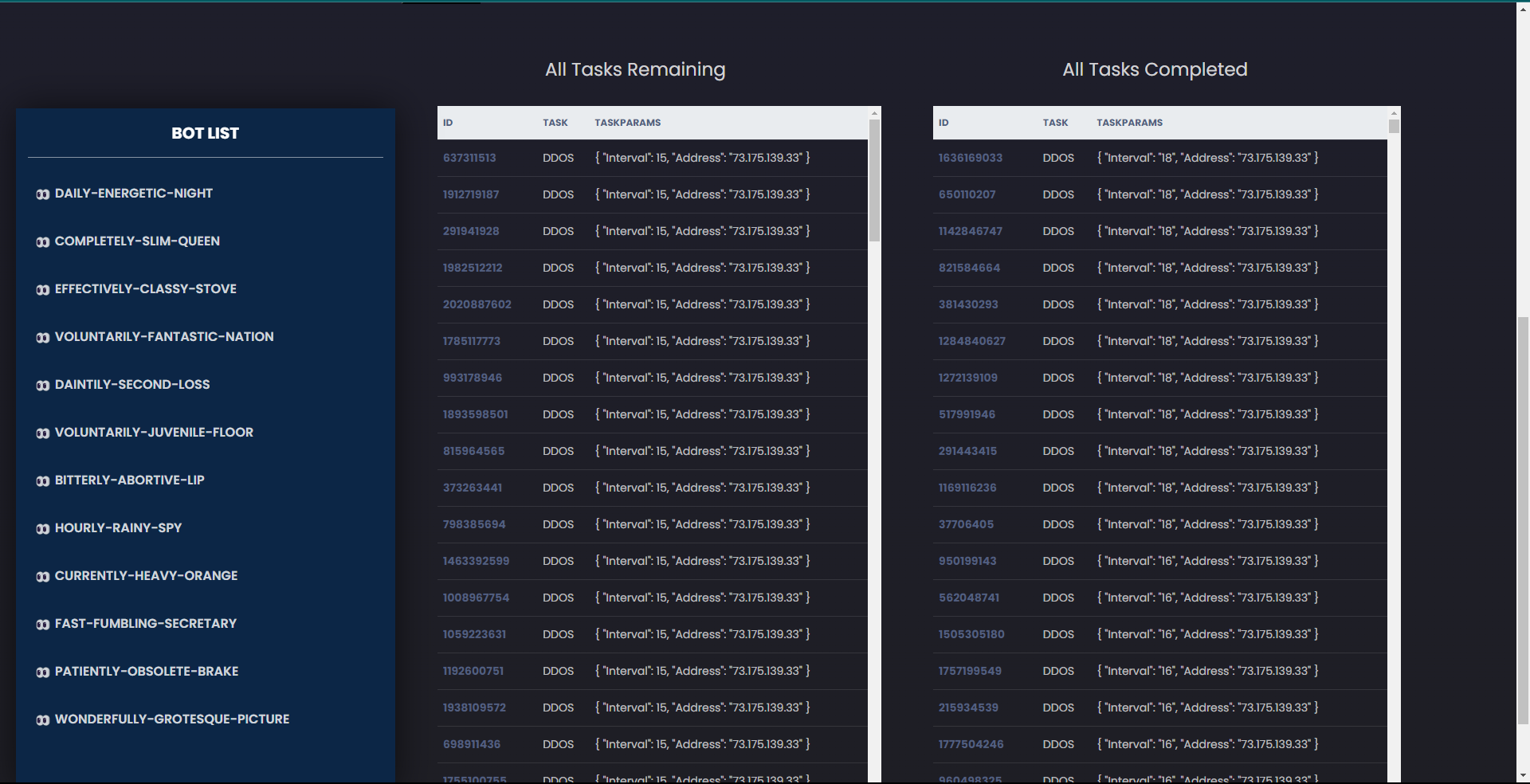
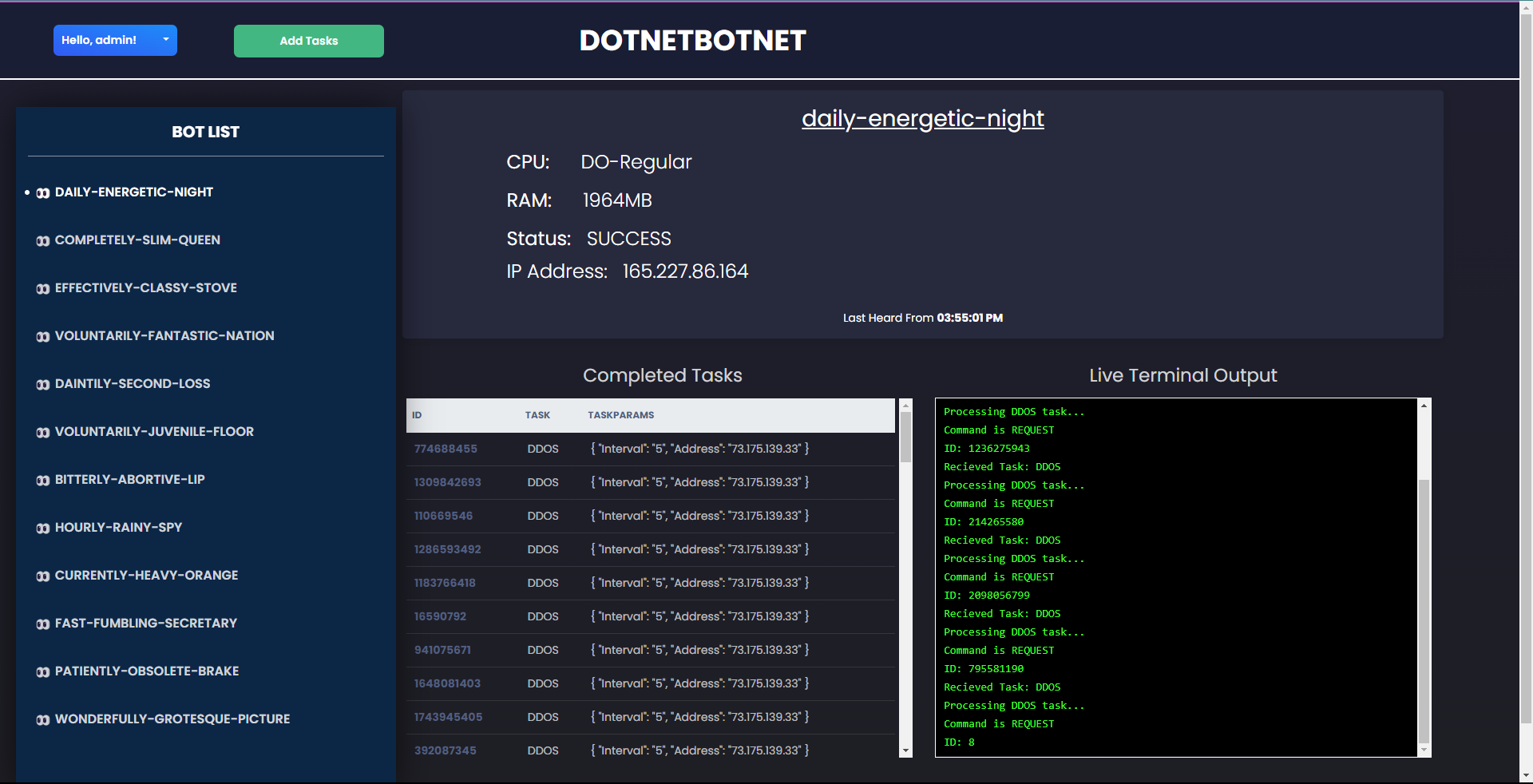
.NETBotNet is a botnet that was created for a Hackathon competition in the Fall of 2023. The project consists of three pieces: a C2 control server, a bot program (referred to as workers), and a web hosted user interface. The C2 server was developed using the .NET Core framework, along with the use of the ASP.NET framework for the development of the API, and it handles all requests made from the user interface and distributes them to the desired workers. The bot program was developed in C++, has functionality for both Windows and Linux based machines, and performs all tasks received from the C2 server. Finally, the web hosted user interface was developed using the Vue.js framework and is where all requests are made to the C2 server. As of now, the botnet can solely send out DDOS attacks to specified machines, or all machines that are connected to the server through their worker, and the team behind .NETBotNet have no plans to continue any further development of the project. Below, you can find some screenshots of the user interface to get a better idea of how the botnet is managed: